BEC is less frequent, involves more attacker craftsmanship, and is more impactful.BEC and VEC are less frequent but potentially more impactful than phishing. (BEC targets employees within an organization, while VEC relies on a compromised vendor account to then target the vendor’s customers or suppliers.)In BEC, VIP impersonation is used in 43% of attacks at small enterprises, but only 7% at large enterprises. Lateral attacks within an organization, where one compromised account targets another account, is the reverse: less than 1% at small organizations rising to more than 23% in large organizations. Noticeably, higher education is especially susceptible to such lateral attacks, where 33% of the BEC attacks are lateral, “Highlighting,” writes Abnormal, “how open, high-turnover environments create ideal conditions for internal spread.”Image Credit: Abnormal AIThe precise methodology used in a BEC attack changes with the size of the company: lateral compromise is effectively nil in small companies, increasing with the size of the company; while VIP/executive impersonation decreases with the size of the company.Nearly 40% of all BEC attacks exploit the trust employees place in colleagues, executives, and internal departments. Forty-five percent of these attacks impersonate a named non-executive colleague. Generic impersonations (“the fake IT helpdesk notice, the HR benefits update, the payroll system alert”) follow at 36.7%. These succeed, comments Abnormal, “Because employees are conditioned to act on communications from internal systems without scrutinizing who actually sent them.”The VEC subtype of BEC is now more common than BEC personal impersonation itself. Invoice fraud dominates VEC in North America, accounting for 42% of VEC campaigns. In EMEA procurement-stage pretexts dominate at 41% of campaigns, demonstrating that geographic business practices are incorporated into attack methodologies.“What makes VEC especially difficult to defend against is that billing and payments are a routine part of the vendor-customer relationship, discussed over email every day. Consequently, malicious messages seemingly from vendors requesting changes to banking information or large fund transfers may not be immediately flagged as suspicious,” warns Abnormal.What is very clear from Abnormal’s analysis is that the old hap-hazard typo-strewn ungrammatical email attack is now assigned to the bin of history. Today we have finely targeted attack campaigns targeting common workflows with sophisticated pretexts and evasion. The report makes no mention of criminal use of AI being used in this new quality of attack (it would be impossible to quantify), but it is undoubtedly an important element.The report does, however, clearly suggest that defensive use of AI can help defend against this quality of attack. “Closing that gap requires AI that analyzes identity, context, and content to build behavioral baselines for every employee and vendor in an enterprise’s cloud environment. That’s what makes it possible to flag the moments when an attack tries to pass as business as usual—before an employee ever has the opportunity to engage.”What is source for the goose must definitely be used as source for the gander.
BEC and VEC are less frequent but potentially more impactful than phishing. (BEC targets employees within an organization, while VEC relies on a compromised vendor account to then target the vendor’s customers or suppliers.)In BEC, VIP impersonation is used in 43% of attacks at small enterprises, but only 7% at large enterprises. Lateral attacks within an organization, where one compromised account targets another account, is the reverse: less than 1% at small organizations rising to more than 23% in large organizations. Noticeably, higher education is especially susceptible to such lateral attacks, where 33% of the BEC attacks are lateral, “Highlighting,” writes Abnormal, “how open, high-turnover environments create ideal conditions for internal spread.”Image Credit: Abnormal AIThe precise methodology used in a BEC attack changes with the size of the company: lateral compromise is effectively nil in small companies, increasing with the size of the company; while VIP/executive impersonation decreases with the size of the company.Nearly 40% of all BEC attacks exploit the trust employees place in colleagues, executives, and internal departments. Forty-five percent of these attacks impersonate a named non-executive colleague. Generic impersonations (“the fake IT helpdesk notice, the HR benefits update, the payroll system alert”) follow at 36.7%. These succeed, comments Abnormal, “Because employees are conditioned to act on communications from internal systems without scrutinizing who actually sent them.”The VEC subtype of BEC is now more common than BEC personal impersonation itself. Invoice fraud dominates VEC in North America, accounting for 42% of VEC campaigns. In EMEA procurement-stage pretexts dominate at 41% of campaigns, demonstrating that geographic business practices are incorporated into attack methodologies.“What makes VEC especially difficult to defend against is that billing and payments are a routine part of the vendor-customer relationship, discussed over email every day. Consequently, malicious messages seemingly from vendors requesting changes to banking information or large fund transfers may not be immediately flagged as suspicious,” warns Abnormal.What is very clear from Abnormal’s analysis is that the old hap-hazard typo-strewn ungrammatical email attack is now assigned to the bin of history. Today we have finely targeted attack campaigns targeting common workflows with sophisticated pretexts and evasion. The report makes no mention of criminal use of AI being used in this new quality of attack (it would be impossible to quantify), but it is undoubtedly an important element.The report does, however, clearly suggest that defensive use of AI can help defend against this quality of attack. “Closing that gap requires AI that analyzes identity, context, and content to build behavioral baselines for every employee and vendor in an enterprise’s cloud environment. That’s what makes it possible to flag the moments when an attack tries to pass as business as usual—before an employee ever has the opportunity to engage.”What is source for the goose must definitely be used as source for the gander.
In BEC, VIP impersonation is used in 43% of attacks at small enterprises, but only 7% at large enterprises. Lateral attacks within an organization, where one compromised account targets another account, is the reverse: less than 1% at small organizations rising to more than 23% in large organizations. Noticeably, higher education is especially susceptible to such lateral attacks, where 33% of the BEC attacks are lateral, “Highlighting,” writes Abnormal, “how open, high-turnover environments create ideal conditions for internal spread.”Image Credit: Abnormal AIThe precise methodology used in a BEC attack changes with the size of the company: lateral compromise is effectively nil in small companies, increasing with the size of the company; while VIP/executive impersonation decreases with the size of the company.Nearly 40% of all BEC attacks exploit the trust employees place in colleagues, executives, and internal departments. Forty-five percent of these attacks impersonate a named non-executive colleague. Generic impersonations (“the fake IT helpdesk notice, the HR benefits update, the payroll system alert”) follow at 36.7%. These succeed, comments Abnormal, “Because employees are conditioned to act on communications from internal systems without scrutinizing who actually sent them.”The VEC subtype of BEC is now more common than BEC personal impersonation itself. Invoice fraud dominates VEC in North America, accounting for 42% of VEC campaigns. In EMEA procurement-stage pretexts dominate at 41% of campaigns, demonstrating that geographic business practices are incorporated into attack methodologies.“What makes VEC especially difficult to defend against is that billing and payments are a routine part of the vendor-customer relationship, discussed over email every day. Consequently, malicious messages seemingly from vendors requesting changes to banking information or large fund transfers may not be immediately flagged as suspicious,” warns Abnormal.What is very clear from Abnormal’s analysis is that the old hap-hazard typo-strewn ungrammatical email attack is now assigned to the bin of history. Today we have finely targeted attack campaigns targeting common workflows with sophisticated pretexts and evasion. The report makes no mention of criminal use of AI being used in this new quality of attack (it would be impossible to quantify), but it is undoubtedly an important element.The report does, however, clearly suggest that defensive use of AI can help defend against this quality of attack. “Closing that gap requires AI that analyzes identity, context, and content to build behavioral baselines for every employee and vendor in an enterprise’s cloud environment. That’s what makes it possible to flag the moments when an attack tries to pass as business as usual—before an employee ever has the opportunity to engage.”What is source for the goose must definitely be used as source for the gander.
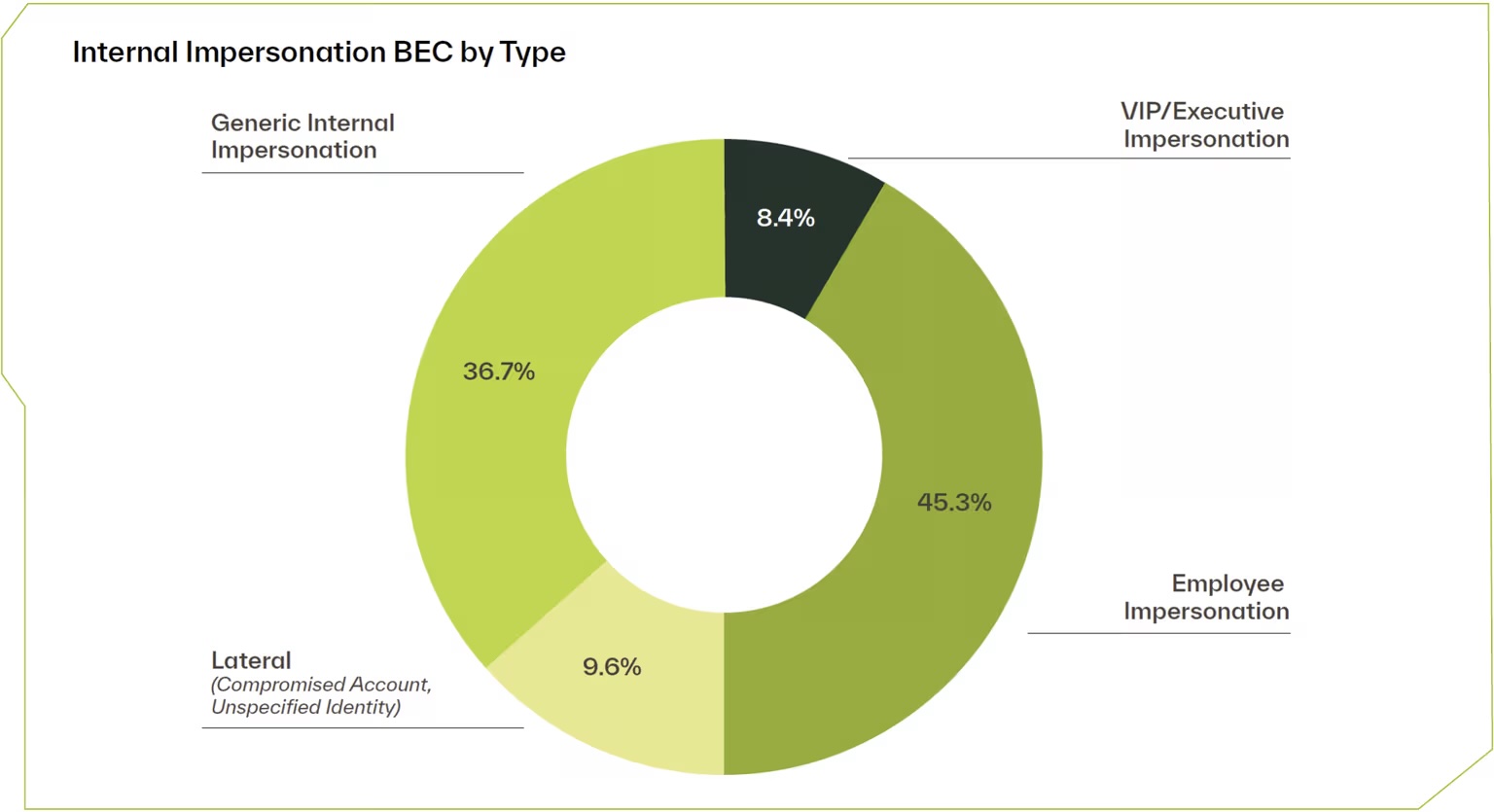
The precise methodology used in a BEC attack changes with the size of the company: lateral compromise is effectively nil in small companies, increasing with the size of the company; while VIP/executive impersonation decreases with the size of the company.Nearly 40% of all BEC attacks exploit the trust employees place in colleagues, executives, and internal departments. Forty-five percent of these attacks impersonate a named non-executive colleague. Generic impersonations (“the fake IT helpdesk notice, the HR benefits update, the payroll system alert”) follow at 36.7%. These succeed, comments Abnormal, “Because employees are conditioned to act on communications from internal systems without scrutinizing who actually sent them.”The VEC subtype of BEC is now more common than BEC personal impersonation itself. Invoice fraud dominates VEC in North America, accounting for 42% of VEC campaigns. In EMEA procurement-stage pretexts dominate at 41% of campaigns, demonstrating that geographic business practices are incorporated into attack methodologies.“What makes VEC especially difficult to defend against is that billing and payments are a routine part of the vendor-customer relationship, discussed over email every day. Consequently, malicious messages seemingly from vendors requesting changes to banking information or large fund transfers may not be immediately flagged as suspicious,” warns Abnormal.What is very clear from Abnormal’s analysis is that the old hap-hazard typo-strewn ungrammatical email attack is now assigned to the bin of history. Today we have finely targeted attack campaigns targeting common workflows with sophisticated pretexts and evasion. The report makes no mention of criminal use of AI being used in this new quality of attack (it would be impossible to quantify), but it is undoubtedly an important element.The report does, however, clearly suggest that defensive use of AI can help defend against this quality of attack. “Closing that gap requires AI that analyzes identity, context, and content to build behavioral baselines for every employee and vendor in an enterprise’s cloud environment. That’s what makes it possible to flag the moments when an attack tries to pass as business as usual—before an employee ever has the opportunity to engage.”What is source for the goose must definitely be used as source for the gander.
Nearly 40% of all BEC attacks exploit the trust employees place in colleagues, executives, and internal departments. Forty-five percent of these attacks impersonate a named non-executive colleague. Generic impersonations (“the fake IT helpdesk notice, the HR benefits update, the payroll system alert”) follow at 36.7%. These succeed, comments Abnormal, “Because employees are conditioned to act on communications from internal systems without scrutinizing who actually sent them.”The VEC subtype of BEC is now more common than BEC personal impersonation itself. Invoice fraud dominates VEC in North America, accounting for 42% of VEC campaigns. In EMEA procurement-stage pretexts dominate at 41% of campaigns, demonstrating that geographic business practices are incorporated into attack methodologies.“What makes VEC especially difficult to defend against is that billing and payments are a routine part of the vendor-customer relationship, discussed over email every day. Consequently, malicious messages seemingly from vendors requesting changes to banking information or large fund transfers may not be immediately flagged as suspicious,” warns Abnormal.What is very clear from Abnormal’s analysis is that the old hap-hazard typo-strewn ungrammatical email attack is now assigned to the bin of history. Today we have finely targeted attack campaigns targeting common workflows with sophisticated pretexts and evasion. The report makes no mention of criminal use of AI being used in this new quality of attack (it would be impossible to quantify), but it is undoubtedly an important element.The report does, however, clearly suggest that defensive use of AI can help defend against this quality of attack. “Closing that gap requires AI that analyzes identity, context, and content to build behavioral baselines for every employee and vendor in an enterprise’s cloud environment. That’s what makes it possible to flag the moments when an attack tries to pass as business as usual—before an employee ever has the opportunity to engage.”What is source for the goose must definitely be used as source for the gander.
The VEC subtype of BEC is now more common than BEC personal impersonation itself. Invoice fraud dominates VEC in North America, accounting for 42% of VEC campaigns. In EMEA procurement-stage pretexts dominate at 41% of campaigns, demonstrating that geographic business practices are incorporated into attack methodologies.“What makes VEC especially difficult to defend against is that billing and payments are a routine part of the vendor-customer relationship, discussed over email every day. Consequently, malicious messages seemingly from vendors requesting changes to banking information or large fund transfers may not be immediately flagged as suspicious,” warns Abnormal.What is very clear from Abnormal’s analysis is that the old hap-hazard typo-strewn ungrammatical email attack is now assigned to the bin of history. Today we have finely targeted attack campaigns targeting common workflows with sophisticated pretexts and evasion. The report makes no mention of criminal use of AI being used in this new quality of attack (it would be impossible to quantify), but it is undoubtedly an important element.The report does, however, clearly suggest that defensive use of AI can help defend against this quality of attack. “Closing that gap requires AI that analyzes identity, context, and content to build behavioral baselines for every employee and vendor in an enterprise’s cloud environment. That’s what makes it possible to flag the moments when an attack tries to pass as business as usual—before an employee ever has the opportunity to engage.”What is source for the goose must definitely be used as source for the gander.
“What makes VEC especially difficult to defend against is that billing and payments are a routine part of the vendor-customer relationship, discussed over email every day. Consequently, malicious messages seemingly from vendors requesting changes to banking information or large fund transfers may not be immediately flagged as suspicious,” warns Abnormal.What is very clear from Abnormal’s analysis is that the old hap-hazard typo-strewn ungrammatical email attack is now assigned to the bin of history. Today we have finely targeted attack campaigns targeting common workflows with sophisticated pretexts and evasion. The report makes no mention of criminal use of AI being used in this new quality of attack (it would be impossible to quantify), but it is undoubtedly an important element.The report does, however, clearly suggest that defensive use of AI can help defend against this quality of attack. “Closing that gap requires AI that analyzes identity, context, and content to build behavioral baselines for every employee and vendor in an enterprise’s cloud environment. That’s what makes it possible to flag the moments when an attack tries to pass as business as usual—before an employee ever has the opportunity to engage.”What is source for the goose must definitely be used as source for the gander.
What is very clear from Abnormal’s analysis is that the old hap-hazard typo-strewn ungrammatical email attack is now assigned to the bin of history. Today we have finely targeted attack campaigns targeting common workflows with sophisticated pretexts and evasion. The report makes no mention of criminal use of AI being used in this new quality of attack (it would be impossible to quantify), but it is undoubtedly an important element.The report does, however, clearly suggest that defensive use of AI can help defend against this quality of attack. “Closing that gap requires AI that analyzes identity, context, and content to build behavioral baselines for every employee and vendor in an enterprise’s cloud environment. That’s what makes it possible to flag the moments when an attack tries to pass as business as usual—before an employee ever has the opportunity to engage.”What is source for the goose must definitely be used as source for the gander.
The report does, however, clearly suggest that defensive use of AI can help defend against this quality of attack. “Closing that gap requires AI that analyzes identity, context, and content to build behavioral baselines for every employee and vendor in an enterprise’s cloud environment. That’s what makes it possible to flag the moments when an attack tries to pass as business as usual—before an employee ever has the opportunity to engage.”What is source for the goose must definitely be used as source for the gander.
What is source for the goose must definitely be used as source for the gander.
Source: SecurityWeek